
🧩 Level 1: Fully Doxxed
Use centralized exchanges such as Binance, Bybit, Coinbase, etc.
Submit passport and ID card for real-name verification
Buy cryptocurrencies with your bank or credit card
as a result of:
Every transfer on the chain can be linked to your real identity through the exchange. You are completely naked on the chain.
🧩 Level 2: Semi Private
Use MetaMask or Phantom Wallet
Keep your own mnemonic
DEX trading via Uniswap or Jupiter
The problem is:
Although you avoid centralized custody, you still top up through KYC exchanges, and your wallet address can still be traced back to your identity by on-chain analysis tools. It seems decentralized, but it is still within sight.

🧩 Level 3: Obscured
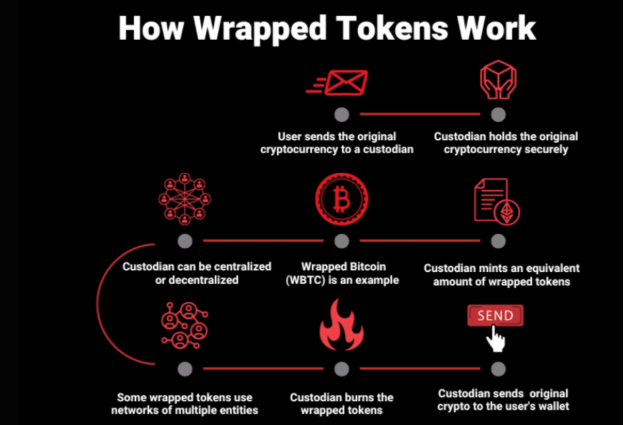
Use cross-chain bridges, currency mixing protocols (such as Tornado.Cash), and create new wallets
Disrupt the transaction path by encapsulating and redirecting tokens between multiple chains
Advantages:
The difficulty of identity association has greatly increased, and it is difficult for ordinary observers to fully restore the track of funds.
But note:
There are still traces of on-chain behavior, and professional analysts can still track you using behavioral patterns.
🧩 Level 4: Shielded
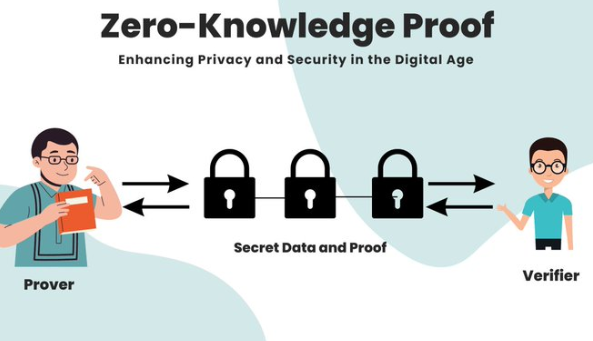
Use privacy protocols such as Aztec, Nocturne, Railgun, Penumbra
These protocols use ZK (zero-knowledge) technology to hide transaction content and transfer objects
Transaction records are “invisible” to on-chain observers
Truly realize anonymous transactions on the chain, and the transfer details are only visible to you and the recipient.
🧩 Level 5: Ghost Mode
Cold wallets are generated completely offline
Purchase assets via cash + P2P or physical crypto ATM
Never used any centralized exchange
No mailbox, no KYC, no metadata leakage
You become a true "digital ghost" - invisible on the chain, off the chain, at the device layer, and at the communication layer.

🎯 Why is this important?
Because regulations are becoming increasingly stringent.
Every year, KYC rules are being strengthened, and even many DEXs will integrate address review. Today you think "privacy doesn't matter", but when you really need it, it may be too late.
As history tells us: the right to privacy is always deprived, not voluntarily given up.
🌐 In addition to the wallet, there are more leaks:
Most users don’t know that
They have already revealed everything about themselves through their browsers.
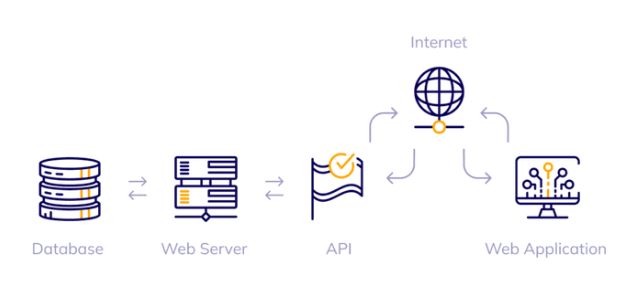
Sign directly in the browser
Ignore VPN or Proxy
Reusing wallet addresses
Use the login account linking tool (Telegram, Discord, Gmail)
Even if you use privacy tools, if your behavior patterns, device fingerprints, and IP addresses are highly consistent, anonymity is just an illusion.
🔐 The real solution: building a layered privacy system
Privacy is not a piece of software or a plugin, but a system of behaviors and tools:
📦 Tool layer suggestions:
VPN / Tor / Mullvad Relay
Brave Browser + uBlock Origin Ad Blocker
Cold wallet (preferably generated offline)
New mnemonics/ New devices
🧠 Behavioral layer suggestions:
Frequently switch wallet addresses
Do not reuse payment addresses
Sign unknown contracts without main wallet
Do not use real-name trading platforms and anonymous wallets on the same device
Be cautious with metadata, such as ENS, avatars, chat logs, habitual operations, etc.
The more predictable you are, the easier it is to profile you.
in conclusion:
The crypto world has never lacked technical tools, but what it lacks is awareness of privacy threats.
True anonymous freedom requires not only "tools" but also a "way of survival".
You won’t always need privacy, but when you do, it’s often too late.
Starting today, start switching your identity level from real name to anonymous, and truly take control of your freedom and security in the decentralized world.

