By Miles Jennings, Scott Duke Kominers, and Eddy Lazzarin, a16z
Compiled by: Glendon, Techub News
As activity and innovation in token-based network models grow, developers are figuring out how to differentiate between different types of tokens — and which ones are best for their business. Meanwhile, consumers and policymakers are trying to better understand the roles and risks of blockchain tokens in applications.
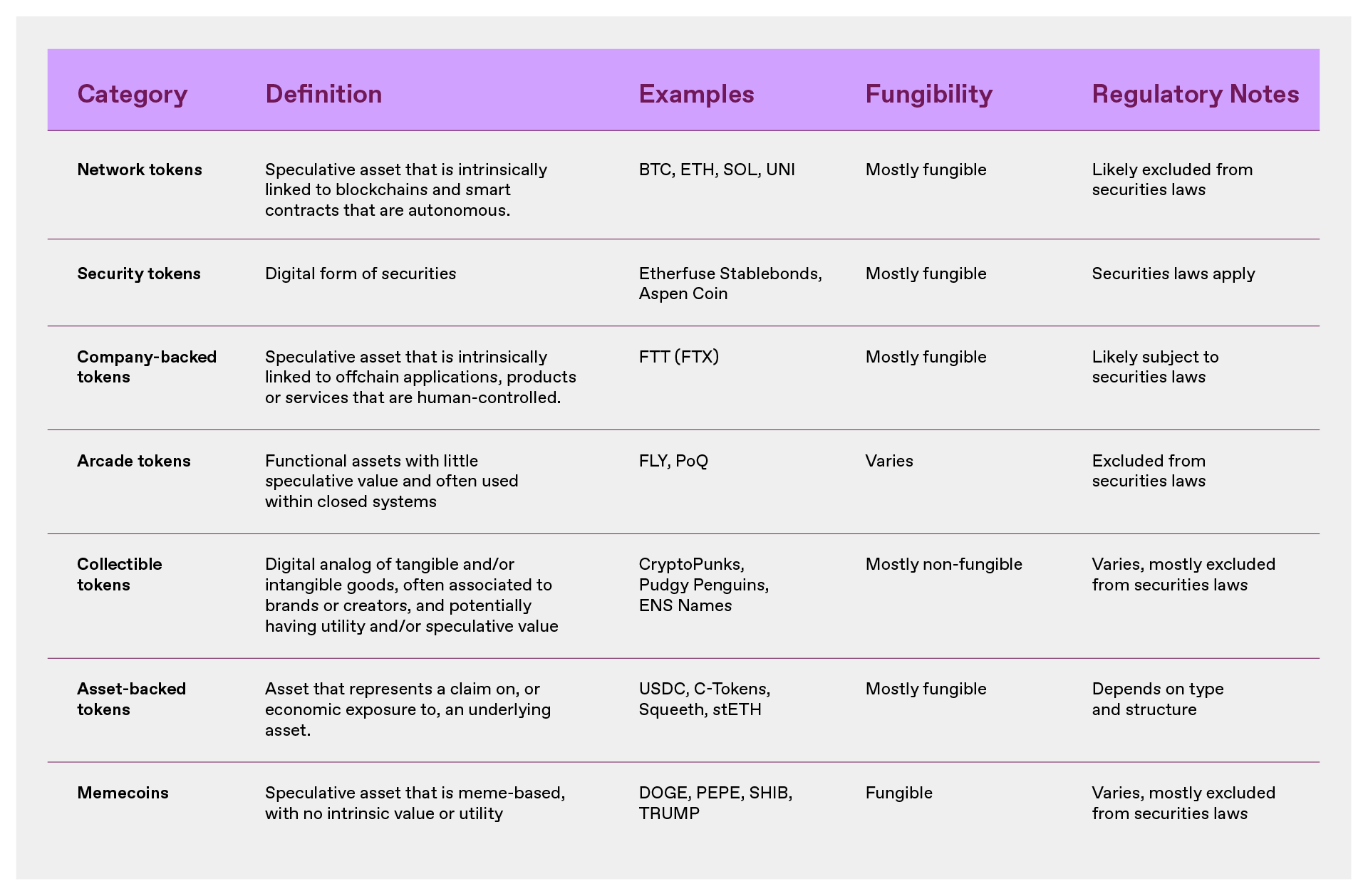
To help sort through the categories of tokens, this article provides definitions, examples, and a classification framework to understand the seven types of tokens that developers most commonly build: Network Tokens, Security Tokens, Company-Backed Tokens, Arcade Tokens, Collectible Tokens, Asset-Backed Tokens, and Memecoins.
Tokens and their characteristics
The essence of tokens is to achieve true digital ownership.
More precisely, a blockchain is a decentralized computer made up of a network of individual computers that maintain a shared ledger—effectively a “ computer in the cloud .” Tokens are data records on these ledgers that track quantities, permissions, and other metadata. Crucially, these data records can only be changed according to the rules encoded in the blockchain, and these rules can be used to grant enforceable rights.
Within this technical framework, there are many details that affect design, functionality, value, and risk:
Programmability
Because tokens are embedded in software, they can be programmed to represent almost anything — any digital form or record of property. This means tokens can be designed as digital stores of value like Bitcoin, productive and consumable assets like Ethereum, collectibles like digital trading cards and gaming items, payment stablecoins like USDC, and even digitized stocks.
Rights and circulation attributes
Some tokens confer rights (such as voting rights or economic rights), while others only allow access to products or network services. Some tokens are freely transferable between users, while others are restricted. Some tokens are fungible, meaning all units are equivalent, while others are non-fungible, meaning they represent unique personal assets (one-of-a-kind, like trading cards or even the Mona Lisa).
These design choices are important because they determine whether a token is a good store of value or medium of exchange; whether it is a productive asset with intrinsic functionality and/or economic value; or whether it is an essentially worthless speculative instrument. At the same time, the characteristics of a token also directly affect its legal characterization.
Therefore, whether you are a blockchain project developer, investor, or ordinary user of tokens, it is crucial to understand the types of tokens - do not confuse Memecoin with network tokens. This article also aims to help investors eliminate this confusion.
Token Type
Network Tokens
Network tokens are intrinsically tied to, and derive their value from, the programmed functionality of a blockchain or smart contract protocol.
Network tokens often have built-in utility; they can be used to operate the network, reach consensus, coordinate protocol upgrades, or incentivize network operations. The networks these tokens are associated with often (and in most cases should) contain economic mechanisms that drive the value of the tokens. These include programmatic buybacks, dividends, and other changes to the total supply of tokens through token creation ("faucets") or destruction ("sinks") to introduce inflationary and deflationary pressures to serve the network.
Network tokens can have trust dependencies similar to commodities and securities. Recognizing this, both the SEC’s 2019 Framework and FIT21 provide that network tokens will be excluded from U.S. securities laws when these trust dependencies are mitigated through the decentralization of the underlying network. The core essence of decentralization is that the system can operate without human control (individuals, companies, or management teams).
Network tokens are best used to bootstrap the creation of new networks , distribute ownership or control of a network to its users, and/or ensure that the network can self-fund its continued and secure operations. Examples of network tokens include BTC, ETH, DOGE, SOL, and UNI. In the context of smart contract protocols such as Uniswap and Aave, network tokens are sometimes also called “protocol tokens” or “application tokens.”
Company-backed tokens
Company-backed tokens are intrinsically tied to an off-chain application, product, or service operated by a company (or other centralized organization). The value of such tokens is derived from this, and they are inherently dependent on the continued operation of the centralized entity.
Like network tokens, company-backed tokens may use blockchains and smart contracts (e.g., to facilitate payments). But because they are primarily associated with off-chain operations rather than network ownership, the company can unilaterally control their issuance, utility, and value. Like “casino tokens” (described below), company-backed tokens often have their own embedded utility. But unlike “casino tokens,” company-backed tokens are speculative.
Given these characteristics—while company-backed tokens do not confer explicit rights, title, or interest on holders like traditional securities—they have a similar fiduciary dependency as securities: their value is inherently dependent on a system controlled by an individual, company, or management team. Therefore, while company-backed tokens themselves are not securities, their trading may be subject to U.S. securities laws when such tokens attract investment.
Company-backed tokens may become a legal category. However, they have historically been used primarily in the United States to illegally circumvent securities laws - attracting investment in applications, products, or services controlled by a company, possibly acting as a substitute for equity or profit interests in that company. Examples of company-backed tokens include FTT, which acts as a profit interest in the FTX exchange, or a hypothetical cloud service provider issuing tokens that enable holders to access cloud services and receive part of the on-chain revenue from such services. BNB is also a classic example of a company-backed token, which evolved into a network token with the launch of Binance Smart Chain. Company-backed tokens are sometimes called "startup tokens" or, given their link to off-chain applications, "application tokens."
That being the case, what is the specific difference between a network token and a company-backed token?
Distinguishing between network tokens and company-backed tokens
It is not easy to distinguish between network tokens and company-backed tokens, as both types of tokens may have utility and derive some value from the blockchain's on-chain functions and the company's off-chain operations. But the distinction is necessary: network tokens and company-backed tokens pose very different risks to holders and should be treated differently under applicable law. So, where is the line?
The only key feature that distinguishes network tokens from company-backed tokens is that their value is primarily derived from the blockchain or smart contract protocol. This feature is important because these systems can operate in an autonomous and decentralized manner, without human intervention or control. Because of this, blockchain-based networks can be truly open: the network effects of the system are captured on-chain and attributed to token holders, and these network effects can in principle be accessed and extended by anyone.
In contrast, company-backed tokens derive their value primarily from off-chain systems or sources that cannot operate autonomously — that is, centralized systems that require human intervention and control. This connection is often obvious, such as when the token price is tied to profits from off-chain applications, products, or services, or when the token has utility in those systems. But it can also be implicit — for example, a token with no real use but riding on the company’s brand may suggest that the company will ascribe value to it.
In either case, if the token is intrinsically tied to a system that does not operate autonomously and its value is primarily (or expected to be) derived from that system, then it is a company-backed token. Due to the lack of autonomy, any associated network (even if seemingly public) is actually closed, just like Web2 social networks controlled by a single company, so the network effects of the token ultimately belong to the company that controls the system, not the users.
Differences in the openness of network designs (closed vs. open) have real economic and regulatory consequences.
Network tokens are associated with open networks that are not controlled by anyone, and are therefore more akin to commodities: they operate in a way that no single party can unilaterally influence or construct the risks associated with the token. This elimination of the reliance on trust distinguishes network tokens from securities. If the network directs value to the token through its functions (e.g. programmatic buybacks and token destruction ), the trustlessness feature is further strengthened.
Company-backed tokens have a similar trust reliance as securities: if the value of a token is derived from a closed network controlled by a single entity, that entity can unilaterally change the expected value of the token. For example, the controlling entity can change the purpose of the token, issue more tokens, or even shut down the entire system at will. This suggests that securities laws should apply when people invest in company-backed tokens.
Two typical cases can further illustrate this distinction:
ETH is a typical network token. It enables holders to trade on the Ethereum network and provides holders with economic rights to the network. The network is decentralized and autonomous (no one or management team controls it). Therefore, the US SEC has clearly determined that securities laws do not apply to ETH.
FTT is a typical company-backed token. Its value is entirely dependent on the continued operation of the FTX exchange, which is itself a centralized exchange operated and controlled by a company. FTX uses part of the exchange's profits to repurchase FTT, thereby driving its economic value. Therefore, FTT is essentially FTX's profit interest - its use and value are controlled by FTX - so it should be subject to securities laws.
However, for tokens that fall between the two extreme cases, the situation may become complicated. But judging whether a token is a network token or a company-backed token can usually be concluded by answering the following three questions:
1. Is the system's network design open?
2. Will the system’s network effects benefit the protocol and token holders?
3. Does the system enable the protocol and token holders to capture value independently?
If the answer to all of the above is “yes”, then theoretically the system can continue to operate (albeit with limited functionality) even if the original development team leaves. This is critical because it means the system can operate without being controlled.
Other examples also help illustrate these concepts, such as the fact that most decentralized exchange (DEX) protocol-related tokens are network tokens, even though the initial development team usually operates the front-end website and off-chain routing software. The reason is:
DEX protocols are usually open networks, and any developer (not just the initial team) can build a front-end website or routing tool based on the protocol.
Key features such as liquidity of a DEX are controlled by the protocol itself, not the development team.
Economic mechanisms built into the protocol (such as the “fee switch”) allow value to flow independently to token holders, allowing the system to continue even if the initial team ceases operations.
Taking games as an example, even if most Web3 games do not run entirely on-chain (relying on off-chain services such as servers), as long as the core assets (props, characters, etc.) are issued on-chain and not controlled by a single party, the system can still be considered an open network. If the protocol designs an economic mechanism that allows value to flow to the token (for example, through the distribution of on-chain transaction fees), then the token is a network token.
In contrast, imagine what would happen if Apple launched an App Store token?
Users who hold tokens can enjoy discounts in the App Store, and can also use them to pay for applications, and the App Store will distribute profits to token holders through smart contracts. However, despite the use of blockchain technology, the value of its tokens is still completely dependent on the closed system controlled by Apple (the App Store), and the use of blockchain does not allow third parties to take advantage of Apple's network effects and establish competing app stores in its system. In addition, the value will come from proprietary off-chain products and services controlled by Apple (the App Store), and even if there are on-chain programmatic economic mechanisms, once Apple closes its store, the value of the token will return to zero. Therefore, the risk profile of such tokens is closer to stocks, which is very different from network tokens and may be subject to securities laws.
Security Tokens
Security tokens represent digital forms of securities and can be traditional (such as company stocks or corporate bonds) or have special features, such as providing an interest in the profits of a limited liability company, a share of an athlete’s future earnings, or even a securitized right to future litigation settlement payments .
Securities typically give holders certain rights, ownership or interests, and their issuers usually have unilateral power to influence or structure the risk of assets. As the US SEC is expected to modernize securities laws to allow on-chain transactions, the number and types of securities being tokenized may increase, which may improve the efficiency and liquidity of the securities market. But even as the category grows, digital securities will still be subject to US securities laws.
Security tokens have been used to raise capital for commercial ventures. Examples of security tokens include Etherfuse Stablebonds and Aspen Coin , which is a fractional ownership interest in The St. Regis Aspen Resort.
Casino Tokens
"Casino tokens" can specifically refer to "functional tokens within a closed scenario" that provide utility within the system and are not used for investment purposes. Such tokens are often used as currencies in the digital economy, such as digital gold in games, loyalty points in membership programs, or points redeemable for digital products and services.
Importantly, casino tokens differ from security tokens, network tokens, and company-backed tokens because they are specifically designed to discourage speculation. For example, these tokens may have an uncapped supply (meaning an unlimited number can be minted) and/or limited transferability; they may expire or lose value if unused, or they may have monetary value and utility only in the system in which they are issued. Crucially, they do not offer, promise, or imply a financial return. Given their inappropriateness as an investment product, casino tokens are generally not subject to U.S. securities laws.
For this reason, casino tokens are best suited for use as money in a digital economy where the issuer gains economic benefits by controlling the monetary policy of that digital economy (i.e. acting as a central bank) and maintaining a stable token value, rather than benefiting from token value appreciation. An example is FLY , which is the loyalty and payment token for the Blackbird restaurant network, and another example is Pocketful of Quarters, an in-game asset. They embody the concept of casino tokens well. Casino tokens are sometimes also called "utility tokens", "loyalty tokens" or "points".
Collectible Tokens
A collectible token derives its value, utility, or meaning from recording ownership of a tangible or intangible good. For example, a collectible token could be a digital simulation or representation of a work of art, music, or literature; a collectible or commodity, such as a concert ticket; a membership in a club or community; or an asset in a game or metaverse, such as a digital sword or a plot of metaverse land .
These tokens are generally non-fungible and often have a utility. For example, collectible tokens can serve as event licenses or tickets; can be used in video games (such as representing a sword); or can provide ownership rights associated with intellectual property. Because collectible tokens are generally associated with finished products or products and do not rely on the efforts of third parties, they are generally not subject to U.S. securities laws.
Collectible tokens are best used to convey ownership of tangible or intangible goods. Many (though not all) "NFT" products fall into this category. Examples include NFTs that convey ownership of digital art or other media; profile pictures ("PFPS") such as CryptoPunks and Bored Apes, and other virtual fashion and branded goods; gaming items; and account records or identifiers (such as ENS domains ).
Some collectible tokens are directly linked to physical products, either providing a digital extension of the physical product experience, such as Pudgy Penguins toys and Generative Goods trading cards; or providing a digital representation of a physical good for easy tracking and/or exchange, such as NFT event tickets and BAXUS’s wine NFTs.
Asset-backed tokens
Asset-backed tokens derive their value from a claim or economic exposure to one or more underlying assets. These underlying assets may include real-world assets (such as commodities, fiat currencies, or securities) or digital assets (such as cryptocurrencies or interests in liquidity pools).
Asset-backed tokens can be fully or partially collateralized and can be used for different purposes: acting as a store of value, a hedging instrument, or an on-chain financial primitive. Unlike collectible tokens, which derive their value from the ownership of a unique good (such as digital art, in-game items, or event tickets), asset-backed tokens function more like financial instruments, deriving their value from their collateral, price peg mechanisms, or redemption rights. However, the regulatory treatment of asset-backed tokens depends on their structure and purpose. Some tokens, such as fiat-backed stablecoins, are generally not subject to U.S. securities laws. Other tokens, such as certain derivative tokens, may be subject to securities or commodity regulation if they represent investment contracts or futures-like instruments.
Asset-backed tokens have many use cases, including:
Stablecoins: pegged to a currency or asset;
Derivative tokens: provide synthetic exposure to underlying assets or financial positions;
Liquidity Provider (LP) tokens: represent claims on pooled assets in decentralized finance (DeFi) protocols;
Deposit Receipt Tokens: Represents the staked or escrowed assets.
The most common examples include USDC (a stablecoin backed by fiat), Compound’s C token (an LP token), Lido’s stETH (a liquidity staking token), and OPYN’s Squeeth (a derivative token that tracks the price of ETH).
Memecoin
Memecoins are tokens with no intrinsic utility or value, typically associated with internet memes or community-driven movements, and with no fundamental connection to a network, company, or application.
Memecoin prices are driven entirely by speculation and related market forces, and are therefore highly susceptible to manipulation. Their primary characteristics are their lack of intrinsic purpose (if they had a purpose, they would no longer be memecoins), their lack of utility, and their resulting zero-sum nature and volatility. Memecoins are generally not subject to U.S. securities laws , but are still subject to anti-fraud and market manipulation laws.
The most typical examples are PEPE, SHIB and TRUMP.
Not all tokens fit neatly into any of the 7 token types above — developers regularly iterate and experiment with new models. For example, social and reputation tokens may be more like “casino tokens” if they are not investable, or more like company backing tokens if they are controlled by a centralized issuer. Tokens can also evolve from one category to another as their characteristics change or new features are added, making classification difficult.
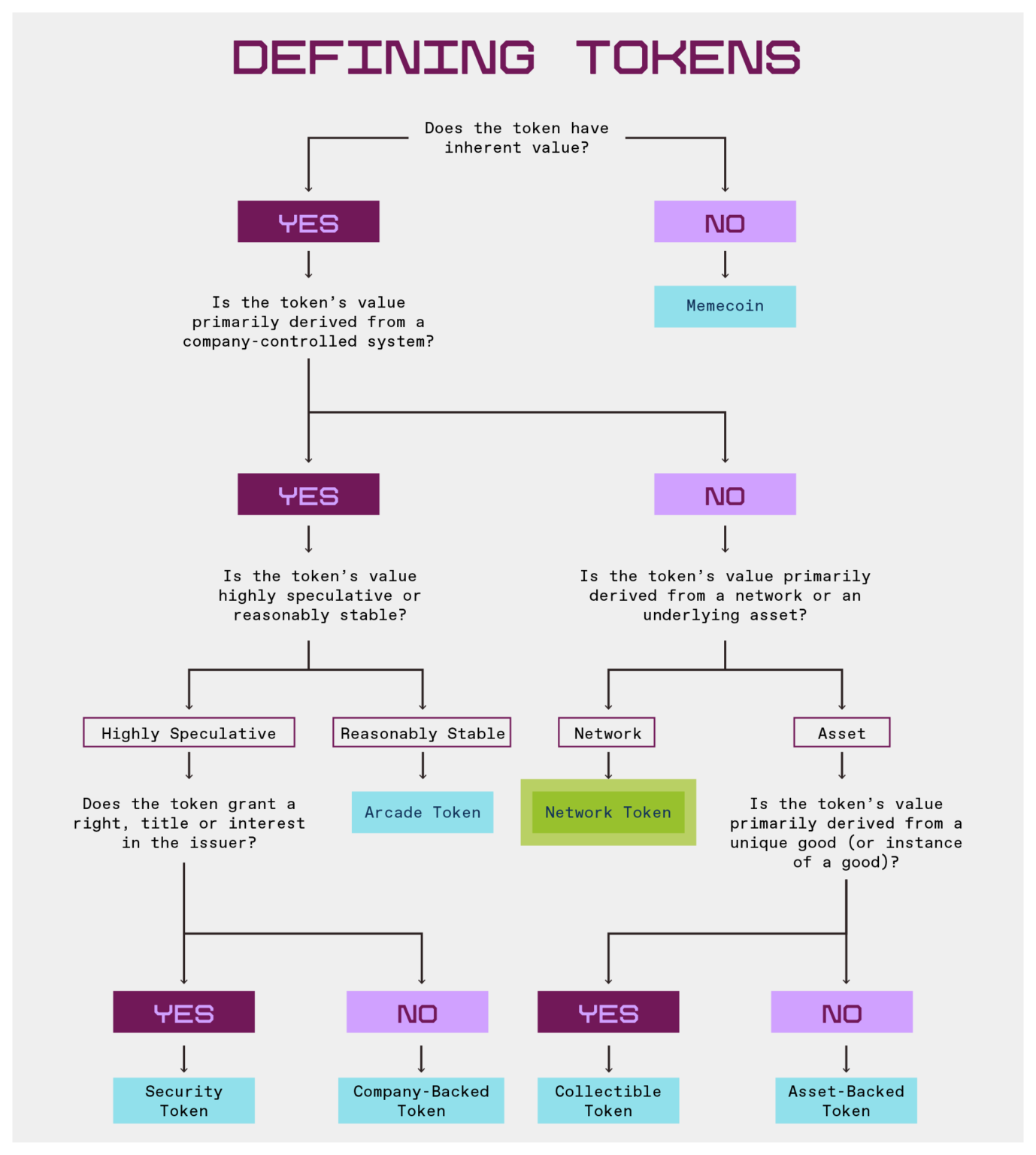
But the defining characteristics that separate these categories are the expected sources of value accumulation, and the following flowchart helps illustrate this: